
If you use LastPass as your password manager, I recommend reading this post in full.
If you know anyone who uses LastPass, forward this to them.
Even if you do know about the LastPass hack, I still recommend you read this, as there will be information here that you may not know about and risks you have not thought of
In case you are not aware LastPass got hacked Back In August 2022 and then AGAIN in November and all customer password vaults have been stolen. This is also not the first time they have been compromised either, it has happened before.
LastPass has been very sketchy about revealing what happened or revealing the seriousness of the hack and waited until December 22nd to put out a statement telling customers their vaults had been stolen, knowing full well that most users would have left for the Christmas holidays and probably wouldn’t read the email or be able to take action.
you can read more about the hack here
My advice is to move away from LastPass ASAP and change all your passwords.
How Serious Is This?
As long as you had a very strong master password on your LastPass account, security experts agree that hackers will not be able to crack it and decrypt your vault, which would potentially take thousands of years or more. If however, you had a weak or moderate master password, then you should probably consider it compromised.
However, the strength of your master password is not the only issue.
There have been numerous issues revealed about how LastPass encrypts data and enforces strong passwords, especially for users who signed up several years ago, when the requirements were much weaker, and LastPass has never prompted or enforced these users to change their weak master password. This means many users do still have weak master passwords that are easy to crack.
It was also discovered by security experts, that LastPass only encrypts the PASSWORD and NOTES fields in the vaults, everything else is in plain text and can be viewed by hackers right now, which is a serious problem. This means all the other data in your vault is compromised, so they know who you are, what company you work for, what websites you use, the usernames of those websites, and any other piece of data you stored in your vault.
If any of the websites/accounts you had stored in LastPass also had weak passwords, the chances of those also being hacked have now also increased.
You can also be sure the hackers will be selling your vault to anyone who wants it on the dark web, so it won’t just be the original hackers trying to get into your vault, it will also be every other hacker and cybercriminal they sell the data to.
The even bigger issue here is that LastPass has now been hacked several times, so obviously their security is not up to scratch, plus the way they have handled the situation is highly unprofessional and unethical. In an attempt to save their reputation and stop customers from leaving in droves, they have been intentionally sketchy with the truth and tried to mislead everyone about what happened, when it happened and how serious it was, meaning they simply cannot be trusted anymore.
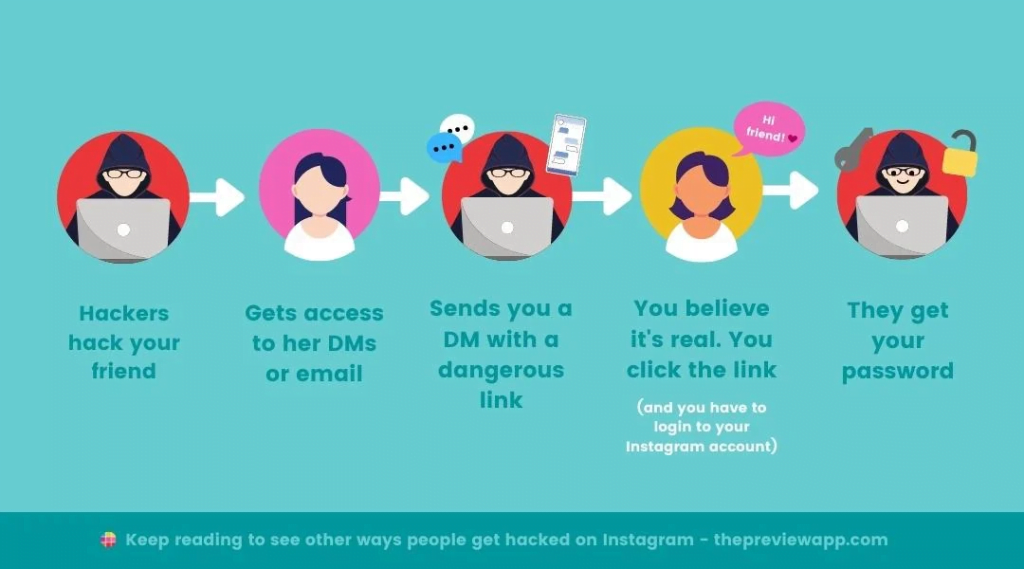
Armed with the non-encrypted information from users’ vaults, it will be very easy for hackers to launch phishing attacks against users, with spoofed and fake emails, appearing to come from the sites they know you use, in an attempt to get you to reveal the passwords for those sites/accounts. So you need to be extra vigilant in checking that every email you receive is really from who it says it is from.

It is not likely that hackers will be going after the average user, there are millions of them, instead, they will be targeting the vaults of high-profile users, CEO’s, MSP’s etc, but this still doesn’t mean you are safe, see the indirect risk warning below.
Please also be aware note that the 2-factor authentication on your LastPass acocunt will not help here, since 2FA only protects the login process on the LastPass app or website. The hackers do not need to log into anything here, they just have an encrypted file that they need to decrypt. So they are simply trying to decrypt the password vaults, which are encrypted with your master password only, so no 2FA is involved.
If you used a password that is made up of information that could be easily gleaned by checking your social media posts and activity etc, such as family member names, date of birth, etc, then these are also easily hacked.
NEVER create passwords made from personal information about you or your family or hobbies etc. Always create random passwords or phrases made from random words. This is the point of using a password manager and why they do this for you.

It is also important to consider how this can indirectly affect you.
Even if your vault does not get compromised, someone else or another company who you do business with (such as me for example), who also has access to any of your systems, websites, or accounts, could have their vault compromised, especially if they had a weak password (my passwords are strong BTW) which in turn compromises you.
It is also highly likely that some websites/businesses you use and trust will end up being hacked as a result of this, due to that company or someone who works there having their LastPass vault compromised.
So by changing all those passwords, you are also protecting yourself from this indirect compromise as well.
What you need to do
You need to get all your data out of LastPass, move to a new password manager, delete your LastPass vault, cancel your account, change all your important passwords and enable 2FA everywhere possible.
1. Change Your LastPass Master Password
Please note that this will not help with the copy of your vault that has been stolen, it will only change the password on your current vault, but if the criminals do manage to crack your master password, then you don’t want them then being able to login to your LastPass account and accessing your live vault as well before you have had a chance to delete it and close your account.
2. Export all your data from LastPass
Click here for instructions on how to do that
If you use LastPass as your 2FA authenticator to generate your One Time Passwords (these are the codes you use for 2-factor authentication), these cannot be exported as they are randomly generated every 60 seconds, what you will get in the export will just be junk.
So you will need to reset the 2FA on all those sites where you are using LastPass as the authenticator and set them up in another authenticator. You can either use whatever new Password Manager you move to or if you prefer to use your mobile device, then I recommend using Microsoft authenticator.
You will need to keep your LastPass account active while you do this since you will need to use it to generate your One Time Passwords to log in to those sites and reset 2FA to begin with.
I recommend importing the exported csv file to Excel, password-protect it, and then save as an .xslx file.
now delete the original csv file and also empty your recycle bin.
This way you do not have all your passwords stored on your computer insecurely in plain text.
2 – Import your data into a new Password Manager
First, you need to pick a new password manager, the best solution will really depend on your requirements.
If you don’t need to share passwords with anyone else, don’t need any bells and whistles, and are happy to store everything on your mobile device, then you can use Microsoft authenticator, as this also has a built-in password manager.
The downside of this is that if you need to log into anything on your PC/laptop or any other device, you will need to manually type those long, randomly generated passwords.
Other popular choices include 1Password, Dashlane, NordPass, Bitwarden, KeePass and many others.
If you use Bitdefender antivirus, then this also has an optional password manager.
I personally have moved to Bitwarden, which has a free plan for personal use and very reasonable pricing on all the other plans. However it’s not the most pretty or intuitive app, so may not be the right choice for the less computer illiterate among you, who may prefer one of the other apps above or something else.
All make it nice and easy to import your LastPass data and provide instructions in their knowledge base on how to do this.
And finally don’t forget to delete that exported file once you have finished with it, and also delete it from the recycle bin too.
TIP: It you press SHIFT while deleting a file, it doesn’t go to the recycle bin.
3. Reset all your 2-factor authentications
As mentioned above, you will need to reset the 2FA on all those sites where you are using LastPass as the authenticator and set them up in another authenticator.
If you don’t do this first, you will no longer be able to get into those sites once you delete LastPass as you won’t be able to generate a OTP, and will need to go through more hoops to reset 2FA and get access to those sites. So decide which option is preferable.
Anywhere that offers 2FA, make sure it’s enabled.
3. Delete your Lastpass account
Once you are sure that you have everything you need from Lastpass, and don’t need to access the OTP’s (One Time passwords) for 2-factor authentication for any of your sites, you can go ahead and close your LastPass account, which will delete your vault.
How to delete your LastPass account.
4. Change all your Important Passwords.
You could work on the basis that your vault will not be decrypted and that you are safe, especially if you had a very strong master password.
Or you may want to go and change all your passwords just in case, don’t forget the indirect compromise I mentioned earlier.
Anywhere where you have 2FA enabled is technically safe, as the password by itself will not let the hackers into that account, and you should get notification of any attempted access.
But you should certainly consider changing passwords on any important site or account where 2FA is not in place.
Such as: your email account (very important, very few email providers have 2FA), hosting account, online banking, social media accounts, website admin, amazon account, and other online stores and anywhere that has your banking or card details stored and could be used to make purchases.
Remember, any website/account that gets hacked, even seemingly insignificant websites, may contain information about you that will then help the criminals/hackers gain access to other accounts of yours, such as your answers to security questions, which are likely going to be the same on every website you use.
Armed with this information, they can then pretend to be you, claiming they have lost their login details, and use the security questions/answers to reset passwords and gain access.
If any 3rd parties also have their own separate logins to anything of yours, such as your email, website, banking, amazon etc, send this information to them, and if they use LastPass, they should also change their passwords too.
5. Be vigilant
As mentioned above, armed with the non-encrypted information from users’ vaults, hackers, cybercriminals, and scammers all around the world will be launching phishing attacks against users, with spoofed and fake emails, appearing to come from the sites they know you use, in an attempt to get you to reveal the passwords for those sites/accounts.
These emails will likely come in the form of warnings about your account being compromised or about this very LastPass hack, telling you to reset your password, and sending you to a fake website.
Since there will also be legitimate emails from those same websites telling you the same thing, you need to check who the email really came from (check the from address) and verify that links in any emails go to the real website (look at the domain name).
The best suggestion is simply to avoid clicking links in such emails, and instead, just go to the website manually by typing the URL, then you know you have gone to the real website.
Also be wary of unusual emails/messages from friends, family, colleagues, staff, and even your boss, as the person sending the messages may be a criminal or scammer who has compromised their email, social media account, etc. If in doubt, always pick up the phone and call that person to make sure it’s actually them you are talking to.
I hope this information was helpful.
Stay Safe






