Cybersecurity researchers uncover MaliBot, a powerful new Android malware that steals passwords, bank details and cryptocurrency wallets from users.

Besides being able to siphon passwords and cookies of the victim’s Google account, the malware is designed to swipe your 2-factor authentication codes from the Google Authenticator app as well as exfiltrate sensitive information such as total balances and seed phrases from Binance and Trust Wallet apps.
The malware has been detailed by cybersecurity researchers at F5 Labs, who’ve dubbed it MaliBot. It’s the latest in a string of powerful malware targeting Android users.
In addition to remotely stealing passwords, bank details and cryptocurrency wallets, MaliBot can access text messages, steal web browser cookies and can take screen captures from infected Android devices. It can also get around multi-factor authentication (MFA) – one of the key cybersecurity defences people can use to protect themselves against cyber criminals.
Like many Android malware threats, MaliBot is distributed by sending phishing messages to users’ phones via SMS text messages (smishing) or attracting victims to fraudulent websites. In both cases, victims are encouraged to clink on a link, which downloads malware to their phone.
So far, researchers have found two malicious websites used to distribute MaliBot – one is a fake version of a legitimate cryptocurrency-tracker app with more than a million downloads from the Google Play Store.
After being downloaded, MaliBot covertly asks the victim to grant accessibility and launcher permissions it requires to monitor the device and perform malicious operations. This includes stealing sensitive information like passwords and bank details, as well as manipulating the device to coerce the victim into giving up additional information – something it does by stealing multi-factor authentication codes.
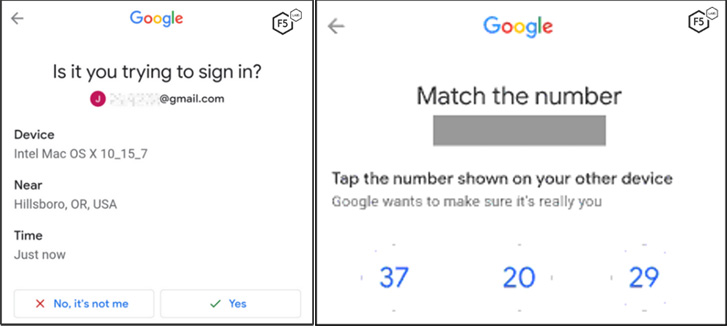
Google Android users are encouraged to uses two-step verification, designed to protect accounts from being accessed by intruders even if the password is known – but the cyber criminals behind MaliBot know this and have devised a way of getting around it.
Once MaliBot has captured credentials on the device, it can bypass multi-factor authentication by using the accessibility permissions, to click the ‘Yes’ button on the prompt asking if the user is trying to sign in. If a user sees this, they might find it suspicious, but the access granted to MaliBot could hide an overlay over the prompt so it isn’t seen.
MaliBot also uses a similar technique to bypass additional protections around cryptocurrency wallets, allowing the attackers to steal any Bitcoin or other cryptocurrencies from accounts linked to the infect Android smartphone.
In addition to stealing sensitive information and currency from the victim, MaliBot is also equipped with the ability to send SMS messages that can be used to infect others with the malware – a tactic similar to that which allowed FluBot malware to become so successful.
Currently, the MaliBot campaign is solely targeting customers of Spanish and Italian banks, but researchers warn that “we can expect a broader range of targets to be added to the app as time goes on”.
While the malware is focused on stealing bank details and cryptocurrency, it’s warned that MaliBot’s powerful capabilities, which allow control over an infected device, could “be used for a wider range of attacks than stealing credentials and cryptocurrency.”
To avoid falling victim to MaliBot or other Android malware attacks, users should be wary of following links in unexpected text messages and should be cautious about downloading apps from third-party websites.
Users should also be aware about the risks associated with enabling accessibility options – while they do have a legitimate use, they’re also widely abused by cyber criminals.
It is also recommended to install a robust cybersecurity and anti-malware solution on all your devices, such as Bitdefender.






